Cybersecurity is no longer a niche skill; it has become a matter of digital hygiene. Cybersecurity has become a major field in the global landscape. Whether you are an IT professional, a student, or someone who wants a protected digital life, choosing the right resources is vital.
However, there are challenges. There are hundreds of cybersecurity books available, and not all of them provide real value to the reader. Guide presents the best cybersecurity books in 2026, covering beginner-friendly introductions, hands-on penetration testing, and advanced cyber warfare topics.
How These CyberSecuirty Books Were Selected
Not every popular book was included here. Each book in this guide has been carefully handpicked based on specific criteria and the reader’s needs.
Here, the selection focuses on real-world practical value, ensuring that readers gain niche-applicable knowledge instead of just theory. In this list, we included books suitable for all levels, from beginners to advanced professionals. The author’s credibility was also taken into account, giving researchers, ethical hackers, and industry specialists priority. Additionally, the curriculum reflects current cybersecurity trends and relevance. Community recommendations were also important considerations.
This approach ensures that readers are not just consuming information but actually building useful ideas regarding cybersecurity skills.
Best CyberSecurity Books for Beginners
In starting of the journey for an individual who is interested in cybersecurity, the following books can help you build a strong foundation without overwhelming technical jargon and complexity.
Book Overview Table (Beginner Level)
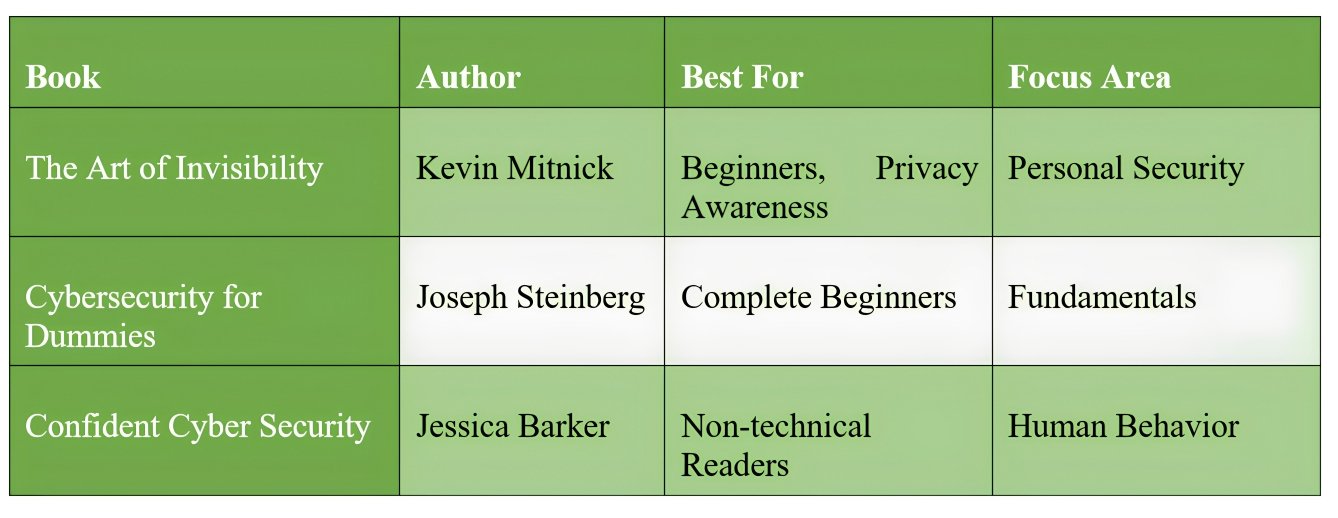
The Art of Invisibility — Kevin Mitnick
The book is available on Amazon as The Art of Invisibility
The Art of Invisibility book explains how personal data is tracked and provides practical ways to protect it.
Digital Privacy: Here, it unveils how corporations and governments track digital activity.
Real-Life Examples: It quotes stories from Mitnick’s hacking career and modern surveillance cases.
Practical Security: Step-wise guides for password security, Wi-Fi safety, and anonymity tools for users.
Empowerment: Teaching readers to be conscious and reclaim control of their personal data.
This book explores how companies track online behaviour and methods to stay anonymous, and tools for everyday digital safety. It is an ideal starting point for understanding real-world cybersecurity beyond theory.
Cybersecurity for Dummies — Joseph Steinberg
The book is available on Amazon as Cybersecurity for Dummies
CyberSecurity for Dummies book provides a simple introduction to cybersecurity without complex technical jargon. The book uses layman’s terms with real-world examples to explain the cybersecurity themes.
Cyber Threats: Starts with explaining attacks featuring malware, phishing, ransomware, and social engineering.
Personal Security: Slowly diving deep into safe browsing habits, password management, and device protection
Business Security: Simple guidance for small and large organizations on data security and networks.
Recovery Plans: Steps to respond to breaches and strategies to restore systems.
Future Trends: This book informs about AI-driven threats, hybrid work risks, and cloud vulnerabilities.
It explains the basics of cyber threats, security best practices, and how vulnerabilities work. It is one of the easiest entry points for readers with no prior background.
Confident Cyber Security — Jessica Barker
The book is available on Amazon as Confident Cyber Security
Confident Cyber Security focuses on the human aspect of cybersecurity. The book focuses on the human aspect and digital hygiene of the user and revolves around how user primary affect cybersecurity.
Human Side of Cybersecurity: Insights into how people get manipulated and how to be protected against social engineering.
Real-World Case Studies: Detailed breakdown of Disney, NHS, Taylor Swift, and Frank Abagnale incidents.
Technical & Physical Security: Fundamentals on how to keep secrets safe and defend systems.
Career Guidance: Insights for aspiring professionals and leaders seeking to strengthen organizational security posture.
Emerging Topics: Discussion on deepfakes, AI, and blockchain security challenges.
It explains the psychology behind cyber-attacks, highlights how human error impacts security, and emphasizes building safer digital habits. It demonstrates that cybersecurity is not only technical but also behavioral.
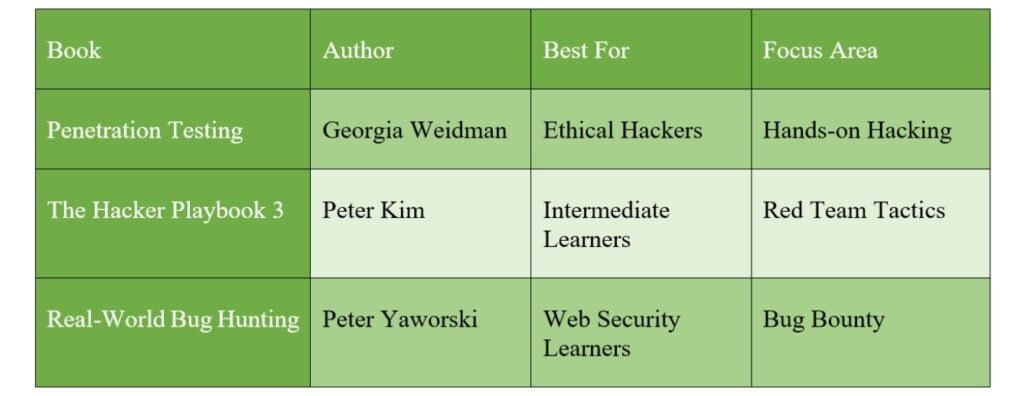
Best CyberSecurity Books for Technical Skills
After understanding the basics, readers can move to more practical and technical knowledge.
Penetration Testing — Georgia Weidman
The book is available on Amazon as Penetration Testing
Penetration Testing provides a practical approach to penetration testing using real tools.
Hands-On Labs: Building a virtual lab with Kali Linux and vulnerable operating systems.
Core Tools: Wireshark, Nmap, Burp Suite, Metasploit Framework
Attack Techniques: Password cracking, wireless attacks, client-side exploitation, and social engineering.
Post-Exploitation: Escalating privileges, pivoting, and maintaining access.
Exploit Development: Buffer overflows, fuzzing, and writing custom Metasploit modules.
Mobile Hacking: Includes Weidman’s Smartphone Pentest Framework.
It includes setting up a hacking lab, exploiting vulnerabilities, and writing basic exploits. It is one of the best resources for transitioning from theory to hands-on practice.
The Hacker Playbook 3 — Peter Kim
The book is available on Amazon as The Hacker Playbook 3
The Hacker Playbook 3 serves as a tactical guide used by professional penetration testers. Book features intermediate ideas for the user, providing a detailed guide on the following themes.
Red Teaming: Simulates real-world advanced attacks to test organizational defenses.
Advanced Offensive Tactics: Exploits, persistence, lateral movement, and custom malware.
Lab-Based Learning: Includes multiple virtual machines, testing environments, and custom THP tools.
Real-World Campaigns: Focuses on practical attack paths and bypassing detection.
It covers red team strategies, advanced attack techniques, and real-world scenarios. It is highly practical and widely used in the cybersecurity industry.
Real-World Bug Hunting — Peter Yaworski
The book is available on Amazon as Real-World Bug Hunting
Real-World Bug Hunting focuses on finding vulnerabilities in real applications.
Bug Bounty Programs: How hackers earn rewards by reporting vulnerabilities.
Real Case Studies: Examples of actual bugs found in companies like Yahoo, Uber, and Shopify.
Techniques Covered: SQL injection, cross-site scripting (XSS), remote code execution, and authentication flaws.
Practical Guidance: How to responsibly disclose vulnerabilities and write effective reports.
Career Pathways: Insights into becoming a professional bug bounty hunter.
It explains bug bounty techniques and common web vulnerabilities, and includes real case studies. It is particularly useful for those interested in earning through bug bounty programs.
Advanced CyberSecurity Books (Professionals & Experts)
These books are designed for experienced professionals working in cybersecurity or IT.
Book Overview Table (Advanced Level)
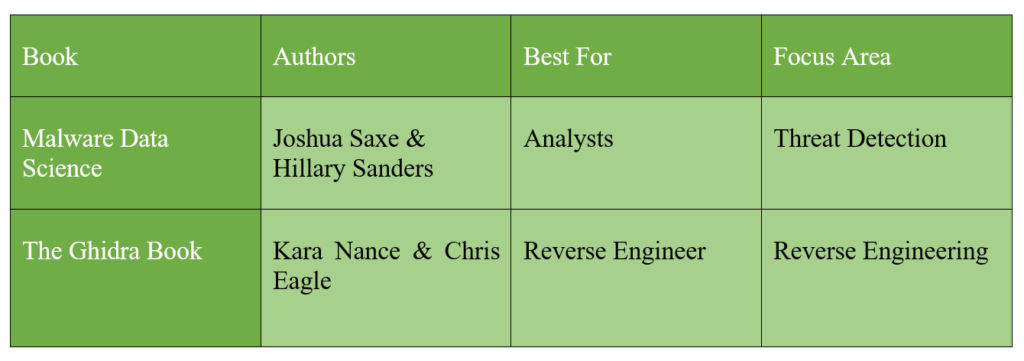
Malware Data Science — Joshua Saxe & Hillary Sanders
The book is available on Amazon as Malware Data Science
Malware Data Science combines machine learning with malware detection.
Machine Learning for Security: Applying data science techniques to detect and classify malware.
Feature Engineering: Extracting meaningful attributes from binaries and network traffic.
Attack Attribution: Using statistical models to identify malware families and threat actors.
Hands-On Examples: Python-based projects for building classifiers and anomaly detectors.
Research-Oriented: Bridges academic machine learning with practical cybersecurity applications.
The Ghidra Book — Kara Nance & Chris Eagle
The book is available on Amazon as The Ghidra Book
The Ghidra Book provides an in-depth understanding of reverse engineering using the Ghidra tool.
Reverse Engineering Fundamentals: Navigate disassembly and use Ghidra’s decompiler.
Malware Analysis: Techniques for analyzing obfuscated binaries.
Extensibility: Build custom analyzers, loaders, and processor modules.
Automation: Script tasks with Python (PyGhidra) and set up collaborative environments.
It covers binary analysis, reverse engineering workflows, and malware investigation.
CyberSecurity Strategy & Management Books
These books are suitable for leadership and decision-making roles.
Book Overview Table
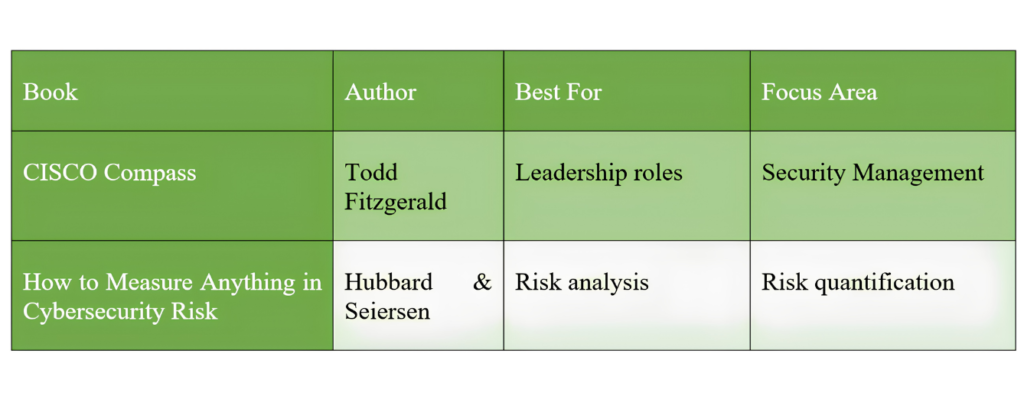
CISO Compass — Todd Fitzgerald
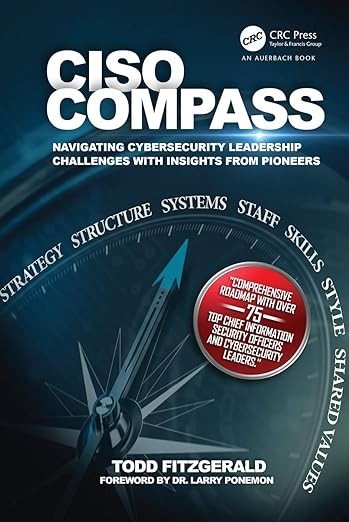
The book is available on Amazon as CISO Compass.
CISO Compass is designed for cybersecurity executives and decision-makers, focusing on leadership and strategy.
Leadership Guidance: Practical insights from over 75 award-winning CISOs and security leaders.
Frameworks: Adapts the McKinsey 7S model (strategy, structure, systems, shared values, staff, skills, style) to cybersecurity leadership.
Boardroom Communication: How CISOs can effectively present cybersecurity strategy to executives and directors.
Program Building: Covers governance, risk management, compliance, and organizational maturity.
Recognition: Winner of the 2020 Cybersecurity Canon Hall of Fame
How to Measure Anything in Cybersecurity Risk — Hubbard & Seiersen
The book is available on Amazon as How to Measure Anything in Cybersecurity Risk.
How to Measure Anything in Cybersecurity Risk book explains how to quantify cybersecurity risks effectively, helping organizations make data-driven decisions.
Quantitative Risk Analysis: Applying statistical and mathematical methods to cybersecurity.
Rapid Risk Audit: A new framework for quick quantitative assessments.
Bayesian Methods: Examples for assessing risk with limited data.
Reputation Damage: Updated research on the real impact of breaches.
Expert Opinion: Methods for combining estimates from multiple experts.
Practical Use Cases: Guidance for IT managers, CFOs, risk officers, and compliance professionals.
Cybercrime, History & Real-World Stories
These books provide real-world insights into cyber warfare and hacking incidents.
Book Overview Table
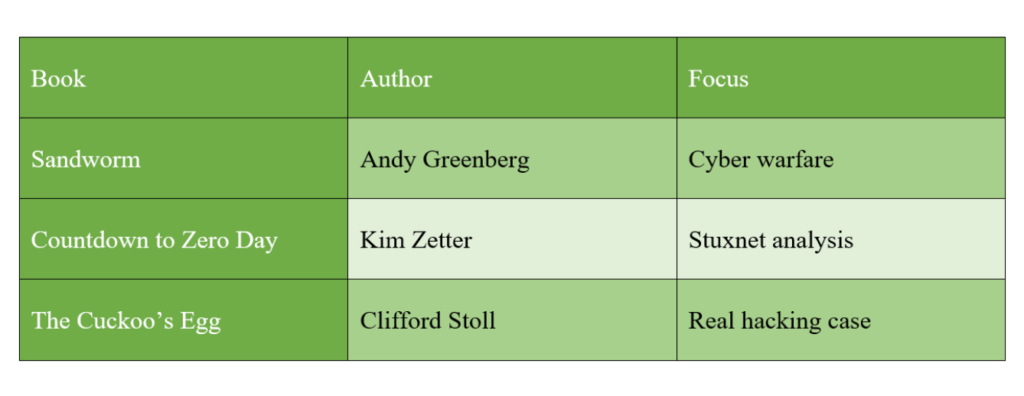
Sandworm — Andy Greenberg
The Book is available on Amazon as Sandworm.
The Sandworm book presents a detailed account of cyber warfare and global cyberattacks. Andy Greenberg is a gripping exposé of Russia’s most dangerous state-sponsored hacking unit.
Cyberwarfare: Chronicles Russia’s GRU hacking unit known as Sandworm.
NotPetya Attack: Details the 2017 malware attack that caused over $10 billion in damages worldwide.
NotPetya Attack: Details the 2017 malware attack that caused over $10 billion in damages worldwide.
Targets: From Ukraine’s infrastructure to global corporations like Maersk and Merck
Investigative Journalism: Combines technical detail with geopolitical analysis, showing how cyberattacks blur the line between war and peace.
Recognition: Winner of the Cornelius Ryan Citation for Excellence from the Overseas Press Club.
Countdown to Zero Day — Kim Zetter
The book is available on Amazon as Countdown to Zero Day
Countdown to Zero Day book provides an in-depth look at the Stuxnet cyber weapon. The book provides a detailed investigative account of the first known cyberweapon and its implications for cyberwarfare and global security.
Stuxnet Malware: The first known cyberweapon, designed to sabotage Iran’s nuclear program.
Cyberwarfare History: How Stuxnet marked a turning point in global security, proving malware could cause physical destruction
Investigative Journalism: Zetter explains the origins of Stuxnet, its discovery, and the geopolitical consequences.
Future Risks: Explores how similar attacks could target critical infrastructure worldwide.
The Cuckoo’s Egg — Clifford Stoll
The book is available on Amazon as The Cuckoo’s Egg
The Cuckoo’s Egg book is a classic real-life hacking investigation story. Book features a real-life account of how a small accounting error led to the discovery of a major international cyber-espionage ring.
True Cyber-Espionage Story: Stoll, an astronomer turned sysadmin, discovers a 75-cent accounting error that leads to uncovering a hacker infiltrating U.S. military networks.
Cold War Context: The hacker, later linked to the KGB, was stealing sensitive information during the late 1980s.
Detective Work: Stoll’s persistence and technical sleuthing highlight early cybersecurity challenges.
Style: Reads like a thriller, blending technical detail with suspenseful narrative.
Social Engineering and Human Hacking Books
Books focus on human manipulation and the psychological aspects of cybersecurity.
Book Overview Table
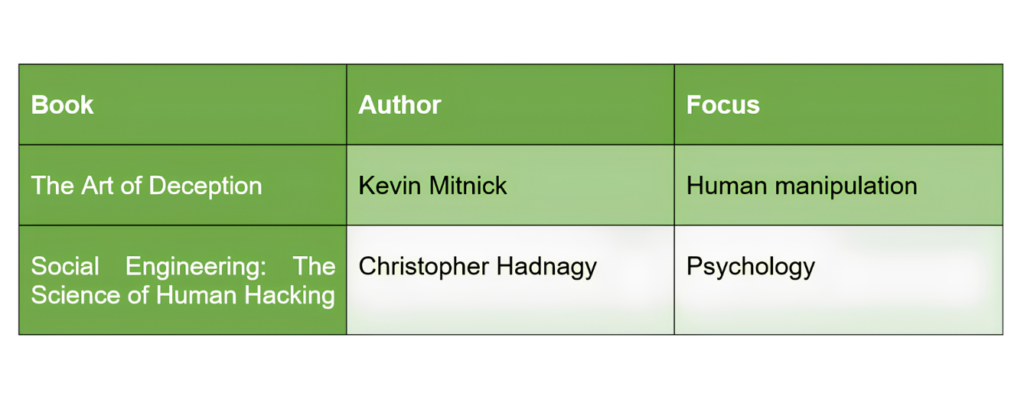
The Art of Deception
The book is available on Amazon as The Art of Deception
The Art of Deception is a foundational book that exposes how attackers exploit trust, authority, and human psychology to bypass technical defenses. The book dives into the key human factors that are crucial in cyberspace, which are given below.
Social engineering: Describes how hackers take advantage of psychological weaknesses in people instead of technological innovations.
True Stories: Actual instances of trickery to get over security measures.
Human Element: Explains why encryption and firewalls are insufficient to prevent manipulation
Prevention: Provides methods for educating staff members and raising awareness to fend off social engineering scams.
Style: It is interesting and approachable since it is written like a true-crime book.
Social Engineering: The Science of Human Hacking
The book is available on Amazon as Social Engineering
Social Engineering is a handbook on the art and science of manipulating human behavior to expose vulnerabilities and strengthen defenses against social engineering attacks.
Human Exploitation: Describes how hackers use psychology instead of technology.
Typical Methods: Pretexting, luring, phishing, and other social engineering techniques.
Case Studies: Actual instances of assaults that got past technological protections.
Scientific insights: The exploitation of emotions and decision-making processes.
Countermeasures: Doable actions to lessen human vulnerabilities and train staff.
Recommended Learning Path (Step-by-Step)
A structured learning approach helps maximize results.
The learning journey should begin with beginner-level books that focus on awareness and foundational concepts. After building a basic understanding, readers should move to technical books that provide hands-on skills. Once comfortable, specialization areas such as malware analysis or penetration testing can be explored. Finally, learning should extend into cybersecurity strategy and risk management.
FAQ
What are the best cybersecurity books for beginners?
Major beginner-friendly books are prominently CyberSecurity for Dummies and The Art of Invisibility here.
Which cybersecurity books are best for hacking?
Penetration Testing and The Hacker Playbook 3 are the best choices among these hacking books.
Can cybersecurity be learned only from books?
These books provide a foundation, but hands-on practice and courses are the real deal for real-world skill development.
What is the best book for ethical hacking?
Penetration Testing is the go-to book for ethical hacking, as it provides a detailed idea about the tools used.
Which books focus on leadership and risk management?
CISO Compass and How to Measure Anything in Cybersecurity Risk are excellent choices for CISOs and managers making decisions.
What are books that explore cyberwarfare and real-world attacks?
Sandworm, The Cuckoo’s Egg & Countdown to Zero Day explore cyberwarfare and covert espionage from real-world instances of attack. They showed an in-depth investigative description of state-sponsored hacking.
Are there any go-to books on the human side of hacking?
Yes, The Art of Deception & Social Engineering are the go-to books describing how attackers exploit human and psychological vulnerability.
Conclusion
The best cybersecurity book depends on your current level and goals. Beginners should start with simple and foundational content. Technical learners should focus on hands-on practice. Professionals should move toward specialization. Consistency is the key. Even a single well-chosen book can significantly change how cybersecurity is understood and applied.
If you are Interested in more cybersecurity-related information, then you are highly recommended to visit Insight Technology’s Website.

